Investigating Window Remote Desktop Connection Events Log
18/03/2023 Thursday
Remote Desktop Connection is a Windows built-in application. It is used to control remote systems by capturing their I/O devices’ signals and transmits them to the controller device using the Remote Desktop Protocol (RDP). RDP is a secure network communications protocol developed by Microsoft.
Digital Forensics Value of Remote Desktop Connection Events Log
All of the incoming/outgoing RDP traffics are stored in event logs’ files, so analyzing it will be allowing the examiners to have a clear picture about the activities performed on a device by any other remote device. Along with the information extracted by the RDC MRU Artifact mentioned in the previous blog, the extracted information from events log artifact is very useful especially because it contains a brief description of each event as well as all of the data associated with that event parsed in a readable way.
Location of Remote Desktop Connection Events Log Artifacts
Remote Desktop Connection Events Log artifacts are found in the following location:
%Systempartititon% \Windows\System32\winevt\Logs
The related information is stored at the following files:
Microsoft-Windows-TerminalServices-LocalSessionManager%4Operational.evtx
Microsoft-Windows-TerminalServices-RDPClient%4Operational.evtx
Microsoft-Windows-TerminalServices-RemoteConnectionManager%4Operational.evtx
Security.evtx
System.evtx
Analyzing Remote Desktop Connection Events Log with ArtiFast
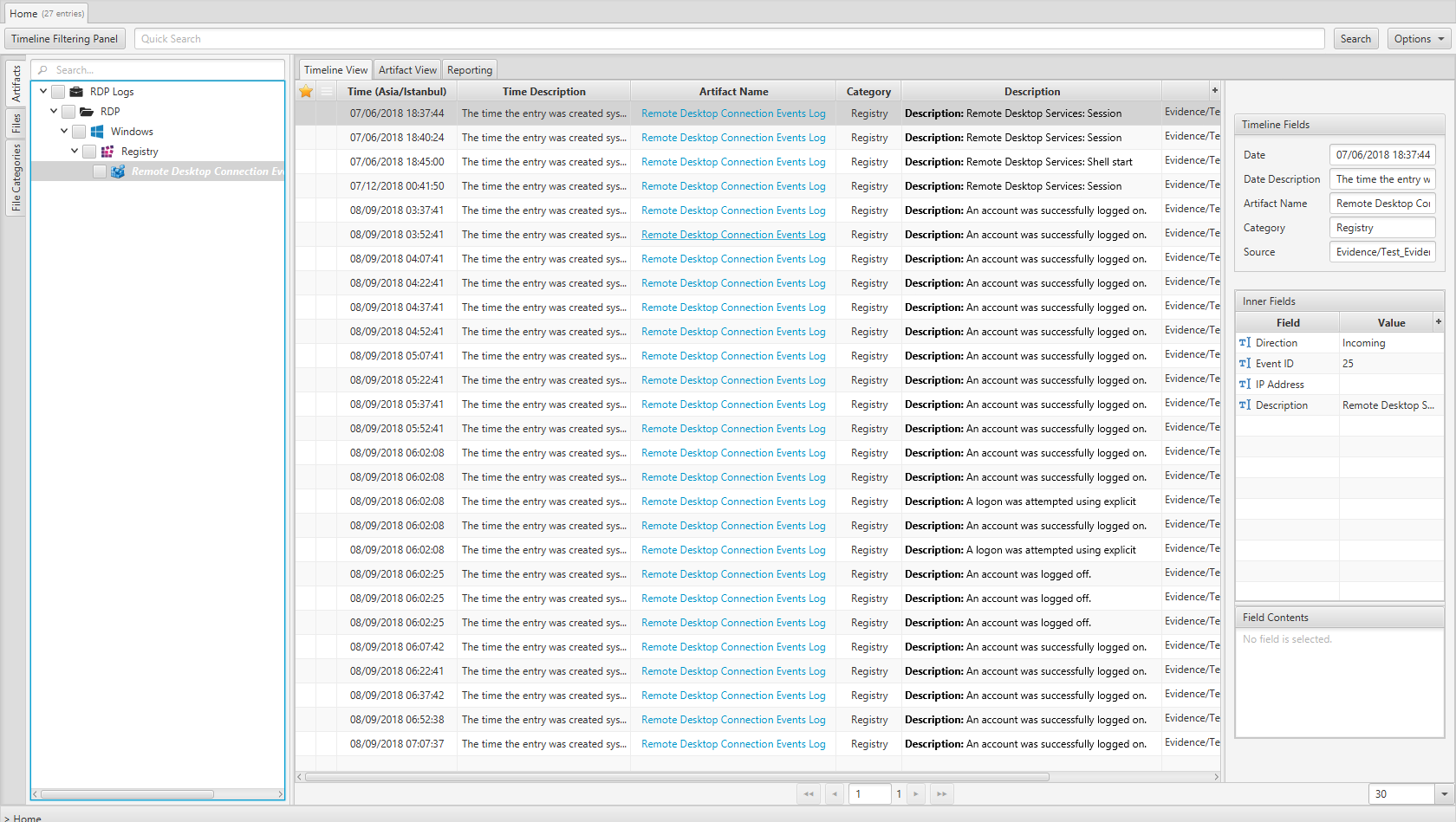
Once ArtiFast parser plugins complete processing the artifact for analysis, it can be reviewed via “Artifact View” or “Timeline View,” with indexing, filtering, and searching capabilities. Below is a detailed description of Windows RDC Events Log artifact in ArtiFast. You can refer to the previous blog for the details related to RDC MRU Artifact.
After you have created your case and added evidence for the investigation, at the Artifact Selection phase, you can select Remote Desktop Connection Events Log artifacts.
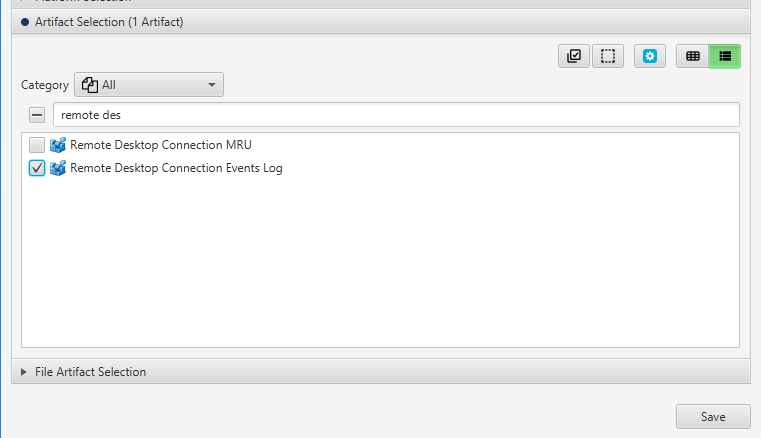
×
Once ArtiFast parser plugins complete processing the artifact for analysis, it can be reviewed via “Artifact View” or “Timeline View,” with indexing, filtering, and searching capabilities. Below is a detailed description of Window Remote Desktop Connection Events Log artifacts in ArtiFast.
Remote Desktop Connection Event Logs Artifact
- Description - The description of the event.
- Event ID - The id of the event.
- Direction - Indicates Whether it is an outgoing or incoming event.
- Created Date/Time - The time and date the entry was created system time.
- Origin IP Address - The origin IP address.
- Destination IP Address - The Destination IP address.
- Event Data- The event data in xml format.
For more information or suggestions please contact: kalthoum.karkazan@forensafe.com
