Investigating WordPad Recent Files
09/09/2022 Friday
WordPad was first introduced in Windows 95. It provides text editing and visualization features similar to Notepad and Microsoft Word. However, it is less feature-rich than Microsoft Word. The default file format for WordPad is Rich Text Format (.rtf), which is a universal clear text document file format.
Digital Forensics Value of WordPad Recent Files Artifact
WordPad stores recently opened filenames and file paths like most text editing software. In Microsoft Office Word, a user can clear the recent files list. However, this feature is not available in WordPad. Therefore, investigating recent files list of WordPad may provide valuable information during a forensic analysis.
Location and Structure of WordPad Recent Files Artifact
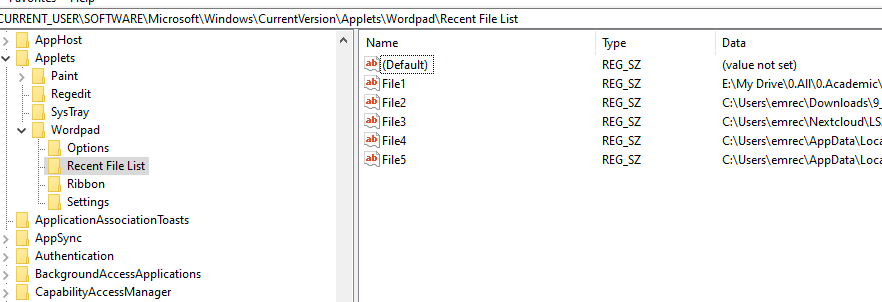
Recent files accessed by the user via WordPad are stored in the Registry at the following location:
HKCU\ \Software\Microsoft\Windows\CurrentVersion\Applets\Wordpad\Recent File List
The recent files accessed do not appear instantly within the Recent File List subkey. The user must close the application window for the changes committed to the Registry key. Like, WordPad Recent File List key stores File# string value, which stores the filename and path details. The order in which the values were accessed can be inferred from the names of the values, as seen in the image below.
Analyzing WordPad Recent Files with ArtiFast Windows
This section will discuss how to use ArtiFast Windows to extract WordPad Recent Files artifact from Windows machines and what kind of digital forensics insight we can gain from the artifacts.
After you have created your case and added evidence for the investigation, at the Artifact Selection phase, you can select the WordPad Recent Files artifact:
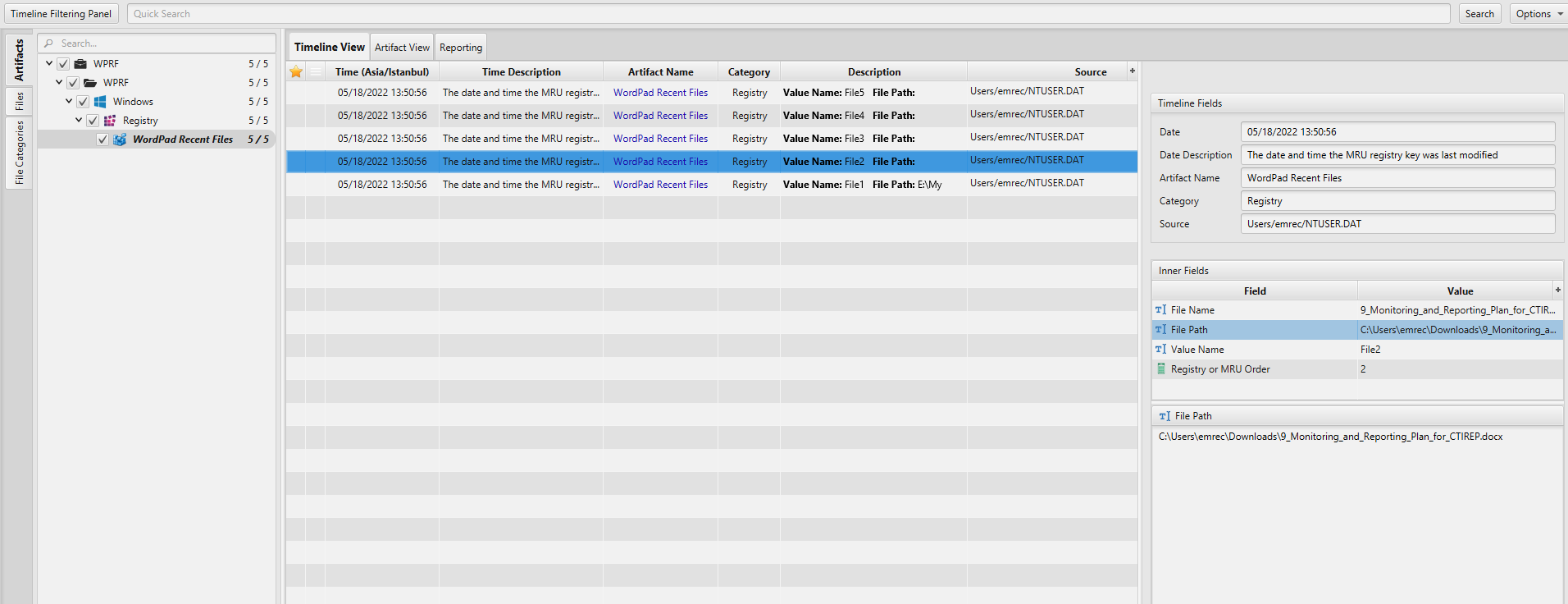
Once ArtiFast parser plugins complete processing the artifact for analysis, it can be reviewed via “Artifact View” or “Timeline View,” with indexing, filtering, and searching capabilities. Below is a detailed description of WordPad Recent Files artifact in ArtiFast.
WordPad Recent Files: This artifact contains information about recent files accessed by the user via WordPad.
- File Name - The name of the file accessed using WordPad.
- File Path - The full path to the file.
- File Modified Date/Time - The date and time the MRU registry key was last modified
- Registry or MRU Order - The order in which the files were accessed. A value of 1 indicates that the file was the most recently accessed.
- Value Name - The value associated with the record within the registry key.
For more information or suggestions please contact: asmaa.elkhatib@forensafe.com
