Investigating VMware Windows Application
25/10/2021 Monday
VMware or Virtual Machine Software is a host workstation that runs on both Windows and Linux operating systems. VMware provides its users with the ability to operate multiple virtual machines on a single physical machine, and each one may run its own operating system.
Digital Forensics Value of VMware Artifacts
Virtual Machine technology has become very popular and is tremendously used in the last years. Their forensics value is that on a par with physical systems since they can perform the same role. In addition, virtual machines make incredibly useful tools with their wide variety of capabilities and different ways of use. In terms of digital forensics, users’ activity trail is recorded by virtual machines and could be tracked by investigators which enables them to view the digital environment in the same way it was originally used by a suspect.
Location of VMware Artifacts
VMware artifacts are stored at the following locations:
C:\Users\Administrator\Documents\Virtual Machines\%MachineName%\vmware*.log
C:\Users\Administrator\Documents\Virtual Machines\%MachineName%\MachineName.vmx
Structure of VMware Artifacts
VMware stores two types of data files, the VMware events logs (*.log) file, which displays the event log for a user, and the VMware Configurations (*.vmx) file, which displays the virtual machine configuration file for a user.
Analyzing VMware Artifacts with ArtiFast Windows
This section discusses how to use ArtiFast Windows to analyze VMware artifacts from Windows machines and
what kind of digital forensics insight we can gain from the artifacts.
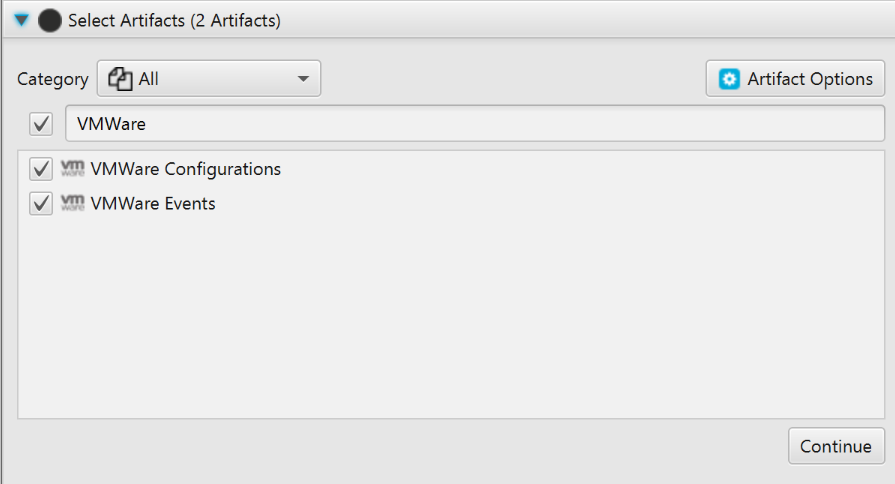
After you have created your case and added evidence for the investigation, at the Artifacts Selection phase,
you can select VMware Artifacts:
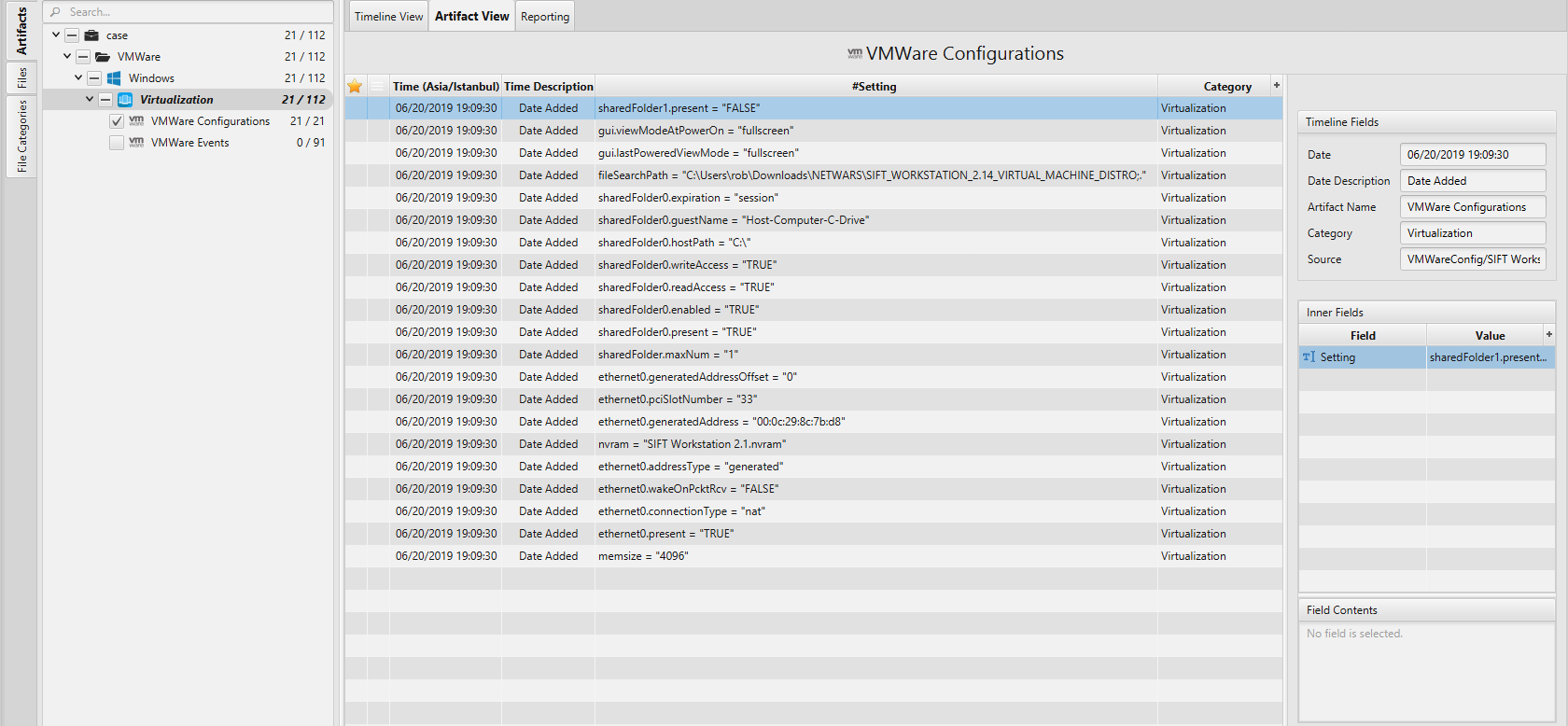
Once ArtiFast parser plugins complete processing artifacts for analysis, it can be reviewed via “Artifact View” or “Timeline View”, with indexing, filtering, and searching capabilities. Below is a detailed description of VMware artifacts in ArtiFast Windows.
VMWare Configurations Artifact
This artifact contains information about the VMware
configurations such as:
- Setting - The configuration.
- Date - The date and time that the event was added.
VMWare Events Artifact
This artifact contains information about the VMware logs and
events such as:
- Event - The event.
- Date - The date and time of the event.
For more information or suggestions please contact: lina.alsoufi@forensafe.com
