Investigating Searched Strings
29/10/2021 Friday
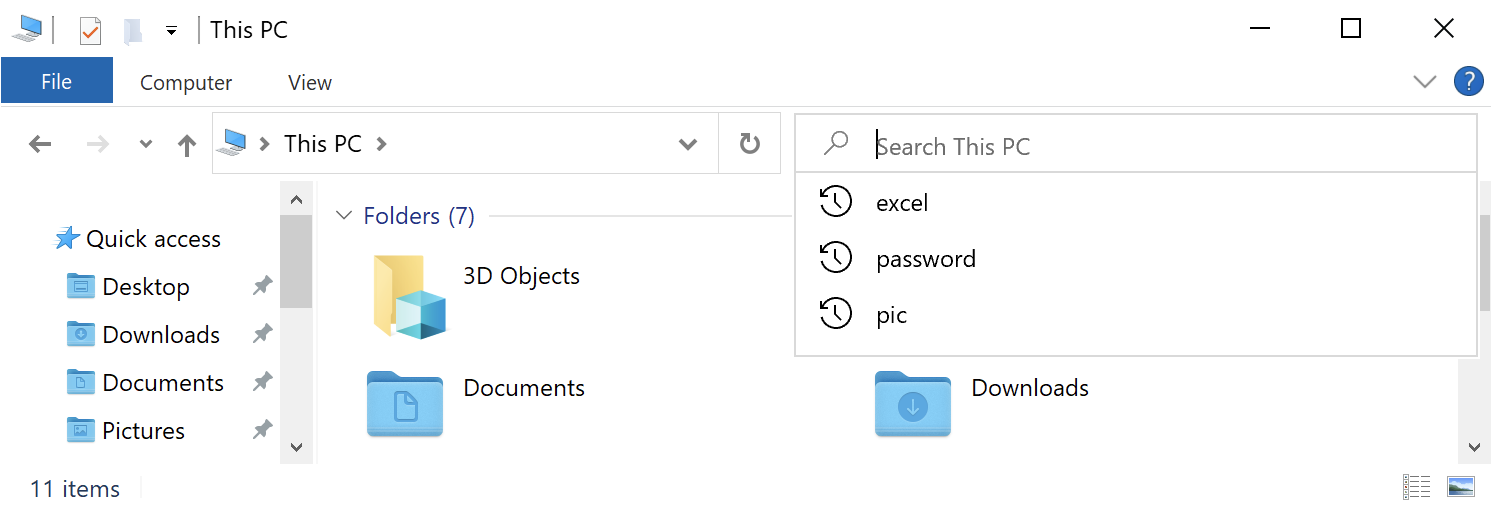
Users often search for things on their devices through the built-in search capability that comes with their
systems. Windows systems maintain a list of the keywords that were searched for on the system in different
locations depending on the version in use.
In recent versions of Windows (Windows 7, 8 and 10), when a user runs a search through the search box of
File Explorer (previously known as Windows Explorer), the searched terms are stored within the Registry
under a key named “WordWheelQuery”.
Digital Forensics Value of Searched Strings Artifact
It might be unlikely for a skilled attacker to search for files by typing into the File Explorer search box. However, WordWheelQuery key may provide valuable insight into the user’s activities on a system. Oftentimes, the terms found within WordWheelQuery key can be completely normal for a particular user but, in other cases, it might indicate a malicious behavior.
Location of Searched Strings Artifact
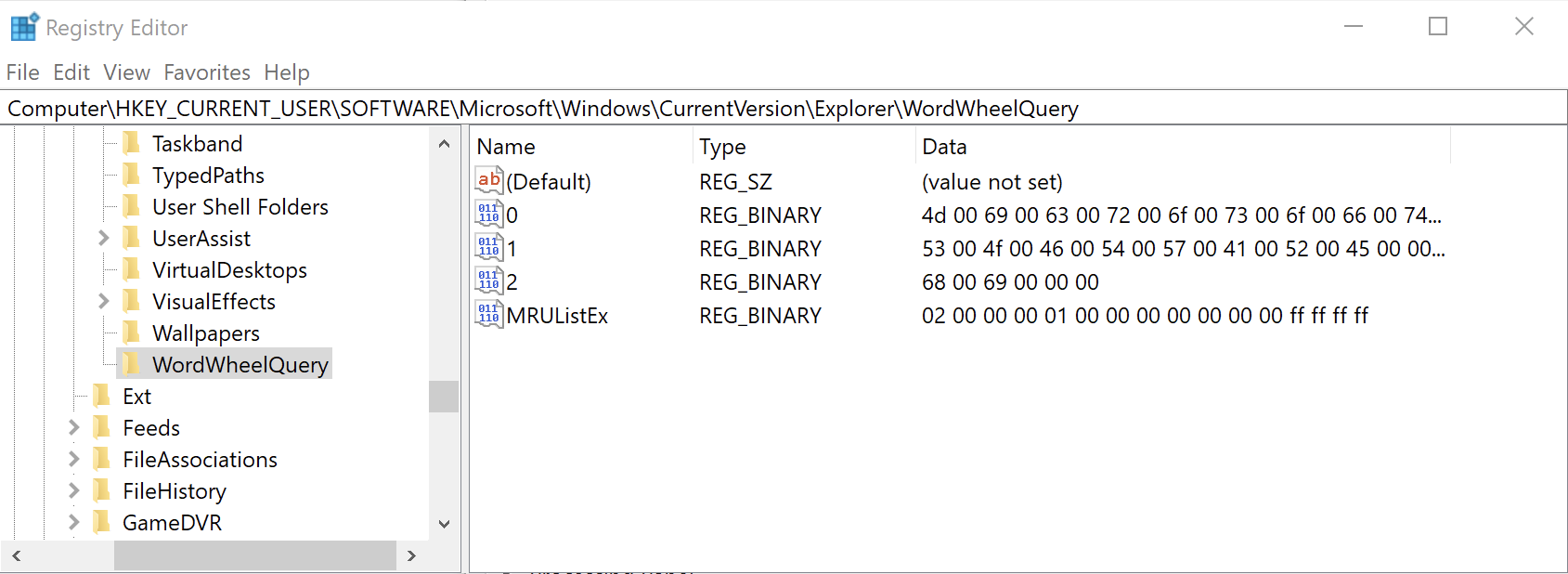
In Windows 7, 8 and 10, information about searches run by the user is stored in the Registry within the
WordWheelQuery key at the following location:
NTUSER.DAT\Software\Microsoft\Windows\CurrentVersion\Explorer\WordWheelQuery
Structure of Searched Strings Artifact
WordWheelQuery key contains several numbered values, and each of these values contains binary data that
corresponds to a searched string. The key also contains a value named “MRUListEx”, which lists the order in
which the keywords were searched by the user.
Analyzing Searched Strings Artifact with ArtiFast Windows
This section discusses how to use ArtiFast Windows to analyze Searched Strings artifact from Windows
machines
and what kind of digital forensics insight we can gain from the artifact.
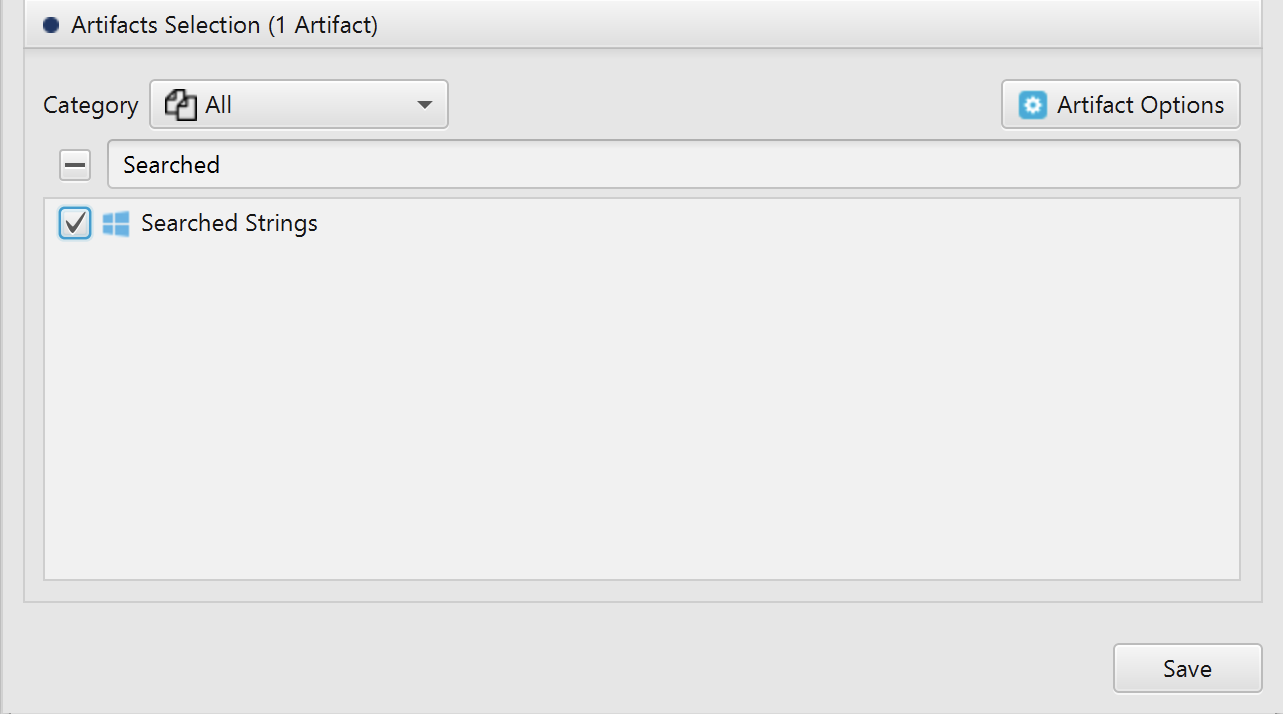
After you have created your case and added evidence for the investigation, at the Artifacts Selection
phase, you can select Searched Strings Artifact:
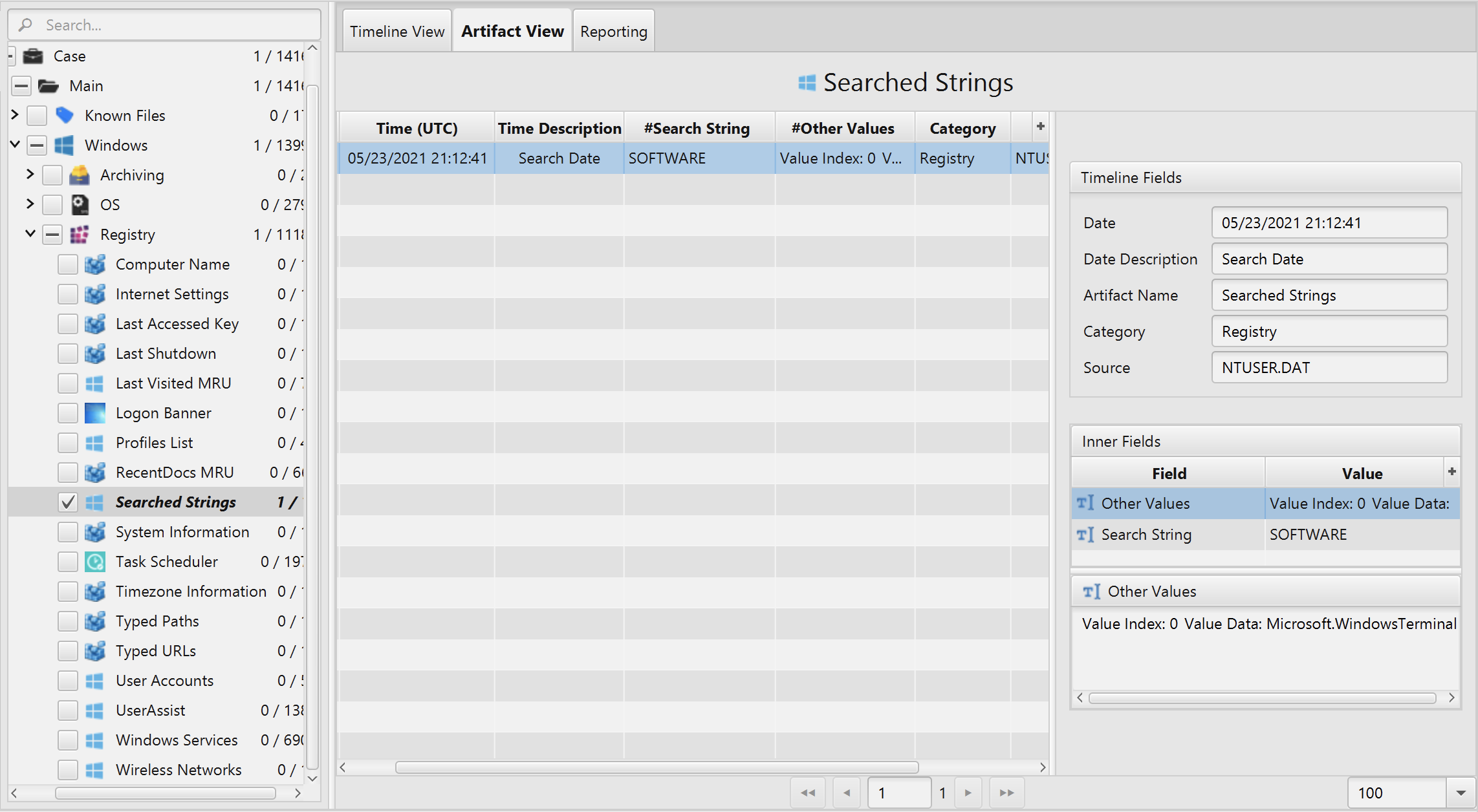
Once ArtiFast parser plugins complete processing artifacts for analysis, it can be reviewed via “Artifact View” or “Timeline View”, with indexing, filtering, and searching capabilities. Below is a detailed description of Searched Strings artifact in ArtiFast.
Searched Strings Artifact
This artifact contains a list of the keywords that were
searched for on the system. The details you can view include:
- Search String - The string searched by the user.
- Search Date - The date and time that the string was searched.
- Other Values - The other strings searched by the user.
For more information or suggestions please contact: asmaa.elkhatib@forensafe.com
