Memory Drivers
17/04/2026 Friday
Windows Memory Drivers artifacts are used to present information about kernel drivers that were loaded or present in memory at the time of acquisition. In this artifact, records for active or recently referenced drivers are extracted from memory analysis data, and values such as the driver name, service key, object address, memory start and end addresses, size, loaded path, and related identifiers are displayed. Because drivers operate in kernel space and are responsible for hardware access, system functions, security controls, and low-level communication, their presence in memory can provide a structured view of the system components that were active when the memory image was captured.
Digital Forensics Value of Memory Drivers
The digital forensics value of Windows Memory Drivers artifacts is
derived from the way loaded kernel drivers are preserved in memory at
the time of capture. The names and paths of drivers can be used to
identify legitimate system components, third-party security software,
virtualisation tools, hardware-related modules, or unexpected drivers
that may require further review. Memory start and end addresses, object
addresses, and size values can be used to examine how driver modules
were mapped in memory and whether unusual loading behaviour is present.
When these records are correlated with process activity, services,
registry entries, persistence artifacts, or security alerts, evidence of
tampering, unauthorised kernel modules, rootkit behaviour, disabled
security controls, or remnants of previously loaded drivers may be
supported or challenged. In incident response and malware
investigations, this artifact can therefore be used to assess
kernel-level activity and the trustworthiness of the running system at
the time the memory image was acquired.
Location of Memory Drivers
For this artifact, information is obtained from DRIVER_OBJECT structures and related kernel driver records that are maintained by the Windows kernel in volatile memory. Each driver object represents a loaded kernel-mode driver, and these structures are allocated and tracked by the I/O manager during system operation. During memory analysis, these in-memory structures are parsed from the acquired memory image and are presented as structured records. As a result, this artifact is not derived from a traditional on-disk artifact.
Analyzing Memory Drivers Artifact with ArtiFast
This section will discuss how to use ArtiFast to extract Memory Drivers
artifact from Windows devices’ volatile data and what kind of digital
forensics insights we can gain from the artifact.
After you have created your case and added evidence for the
investigation, at the Artifact Selection phase, you can select the
Memory Drivers artifact parser:
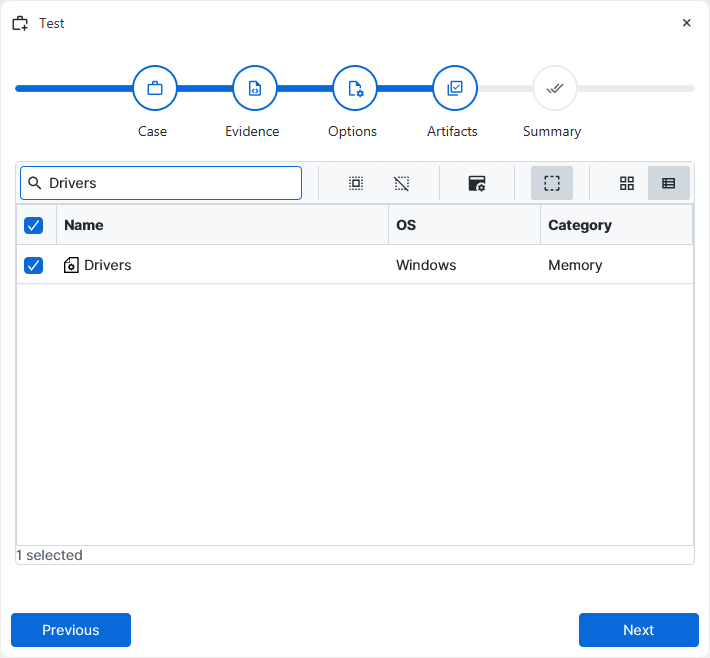
×
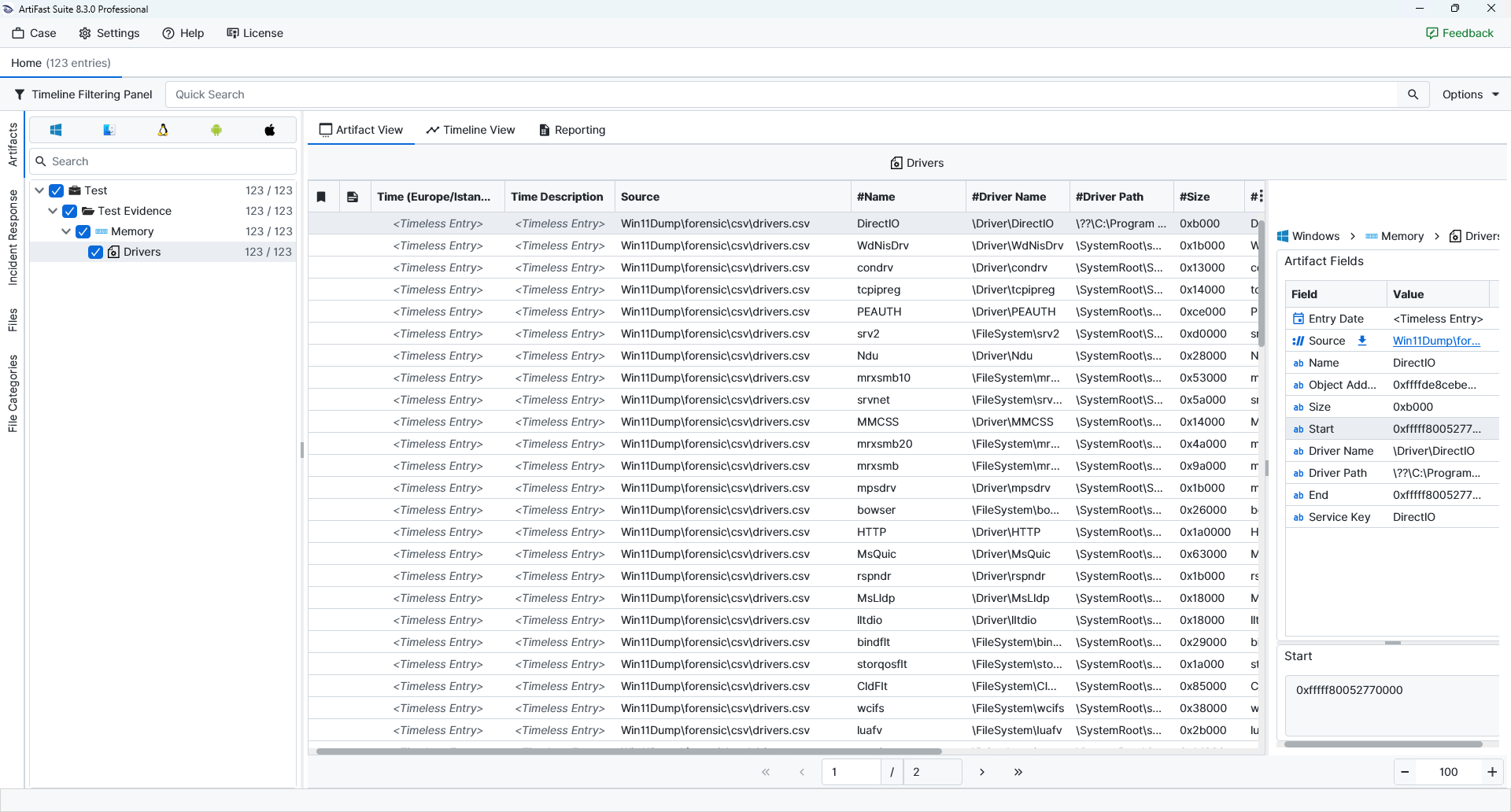
Once ArtiFast parsers plugins complete processing the artifact for analysis, it can be reviewed via “Artifact View” or “Timeline View,” with indexing, filtering, and searching capabilities. Below is a detailed description of Memory Drivers artifact in ArtiFast.
Drivers
- Name : The short driver name is recorded in this field. This value is used as the base identifier for the driver and is typically shown without the full Object Manager prefix.
- Service Key : The service key or service name associated with the driver is recorded in this field. In many cases, this value matches the short driver name.
- Object Address : The memory address of the associated DRIVER_OBJECT structure is recorded in this field. This value identifies the in-memory kernel object representing the driver.
- Start : The starting memory address at which the driver image is mapped is recorded in this field.
- End : The ending memory address of the mapped driver image is recorded in this field.
- Size : The size of the loaded driver image in memory is stored in this field.
- Driver Path : The filesystem path associated with the driver image file is recorded in this field, where available. This path can be used to identify the backing driver file on disk.
- Driver Name : The full internal kernel object name associated with the driver is stored in this field. This value shows the object manager namespace under which the driver is registered.
For more information or suggestions please contact: ali.tora@forensafe.com
