Android Application Operations
28/11/2025 Friday
Android Application Operations is an Android system artifact where
actions related to app permissions are recorded. In this file, it is
stored when a permission was allowed, rejected, or changed, together
with basic details about the app that requested it and how the operation
was handled. During an investigation, this artifact can be used to see
how apps were using or trying to use sensitive features on the device
Digital Forensics Values of Android Application Operations
From this artifact, information can be obtained about when a specific
permission or operation was allowed or rejected for an app, and which
app package was involved. It can also show whether the permission was
granted directly to the app or through a proxy package, and how these
decisions changed over time.
When this data is combined with other artifacts, it helps investigators
build a clear timeline of permission use and spot unusual or suspicious
changes in an app’s behavior.
Location of Android Application Operations Artifacts
Android Application Operations artifacts can be found at the following
locations:
/data/system/appops.xml
Analyzing Android Application Operations Artifact with ArtiFast
This section will discuss how to use ArtiFast to extract Android
Application Operations artifacts from Android machines’ files and what
kind of digital forensics insights we can gain from the artifact.
After you have created your case and added evidence for the
investigation, at the Artifact Selection phase, you can select Android
Application Operations artifact parsers:
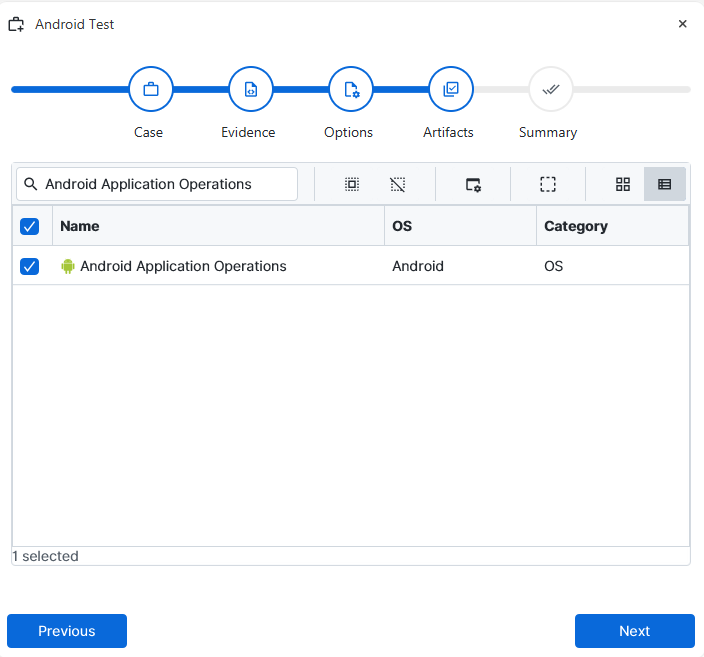
×
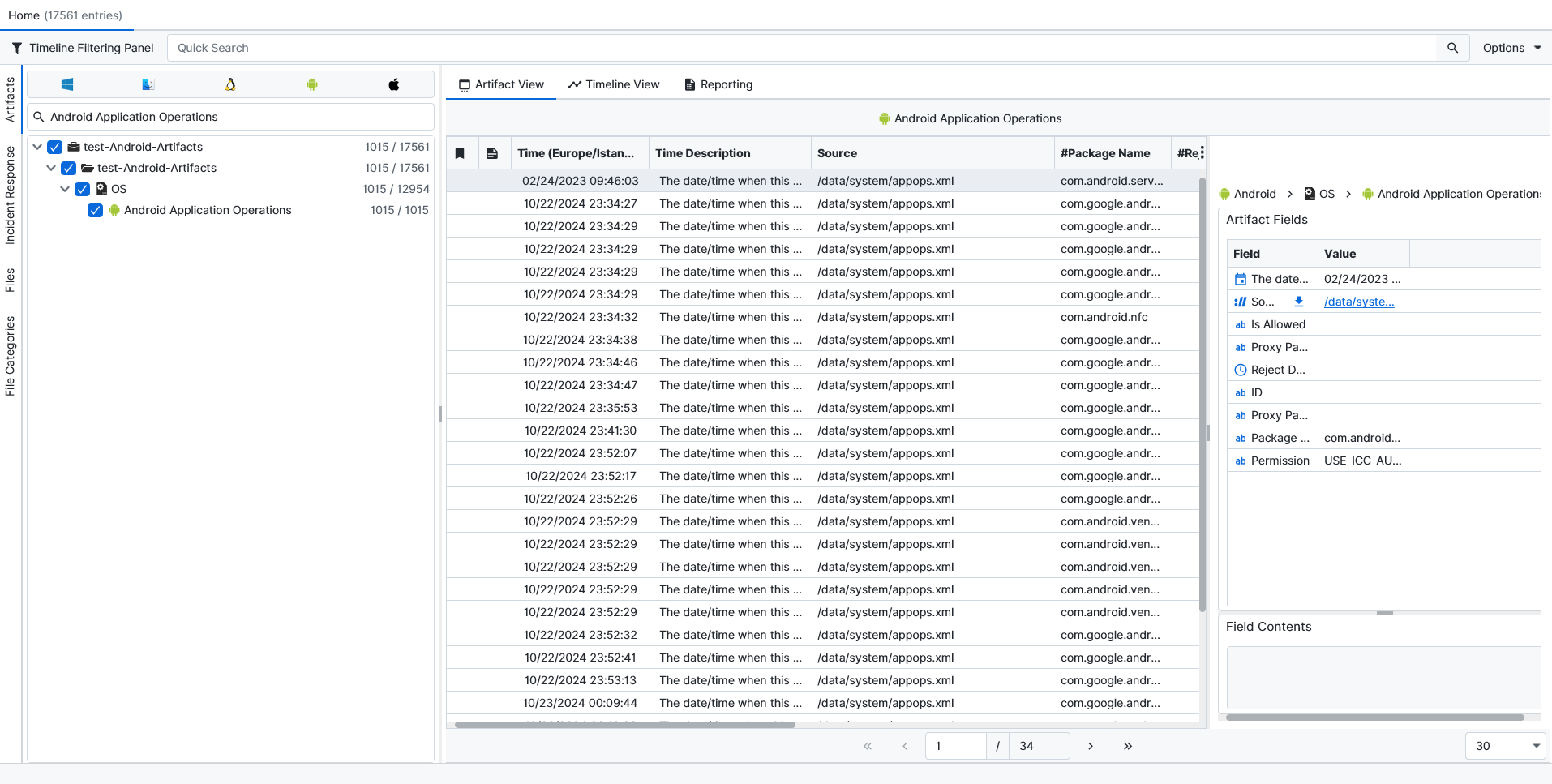
Once ArtiFast parsers plugins complete processing the artifact for analysis, it can be reviewed via “Artifact View” or “Timeline View,” with indexing, filtering, and searching capabilities. Below is a detailed description of Android Application Operations artifacts in ArtiFast.
Android Application Operations:
- Is Allowed: Indicates whether this permission has been allowed or not.
- Proxy Package UID: The unique identifier of the proxy package.
- Reject Date/Time: The date/time when this permission has been rejected to be given to this package.
- ID: The unique identifier for the operation performed under this package.
- Proxy Package Name: The proxy package name.
- Package Name: The bundle name of the application that requested this permission.
- Permission: The permission name.
For more information or suggestions please contact: hamzamm.aljaeba@forensafe.com
